Tableau Server #
Tableau Server connects to Starburst Galaxy or SEP in the same ways as Tableau Desktop.
However, you can publish JDBC or ODBC connector-based data sources and workbooks from Tableau Desktop, and then use them in Tableau Server.
Additionally, installing the Starburst connector, JDBC or ODBC driver, and configuring OAuth clients are different from Tableau Desktop and Tableau Prep Builder.
Starburst connector #
- Install Trino JDBC driver 469 or later if you have not done so.
Download the latest Trino JDBC
driver, and place it in the following
location:
-
Windows: C:\Program Files\Tableau\Drivers
Linux: /opt/tableau/tableau_driver/jdbcDo not store more than one Starburst JDBC driver in this directory. Delete any previous drivers when you update to a newer version.
-
Go to this Tableau Exchange page and download the Starburst connector (named
StarburstJDBC-x.x.x.taco). Save it to the following location:-
Windows: C:\Program Files\Tableau\Connectors
Linux: /opt/tableau/connectors - Restart Tableau Server.
ODBC connector #
-
Download and install the latest Starburst ODBC driver as appropriate for your operating system.
-
Restart Tableau Server.
JDBC connector #
-
Install Trino JDBC driver 469 or later if you have not done so. Download the latest Trino JDBC driver, and place it in the following location:
-
Windows: C:\Program Files\Tableau\Drivers
Linux: /opt/tableau/tableau_driver/jdbcDo not store more than one Starburst JDBC driver in this directory. Delete any previous drivers when you update to a newer version.
-
Restart Tableau Server.
OAuth 2.0 authentication #
To use OAuth 2.0 to connect to SEP or Starburst Galaxy, follow this instruction to generate your own OAuth configuration file, then register OAuth client.
-
Sign in to your Tableau Server site using admin credentials and navigate to the Settings page.
-
Under OAuth Clients Registry, click the Add OAuth Client button.
-
Enter the required information, which should be the same as when you create a OAuth client in your identity provider or in Starburst Galaxy. Click Add OAuth Client, then Save.
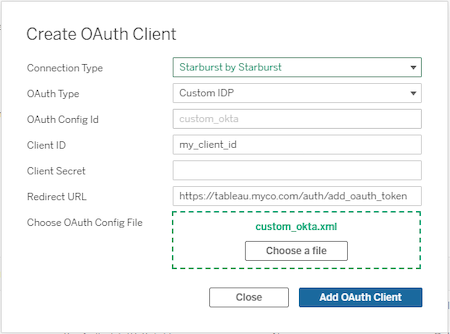
For more information about setting up server level and site level OAuth clients in Tableau Server, see this instruction in Tableau documentation.
Is the information on this page helpful?
Yes
No